Security Operations Center (SOC)

MISSION
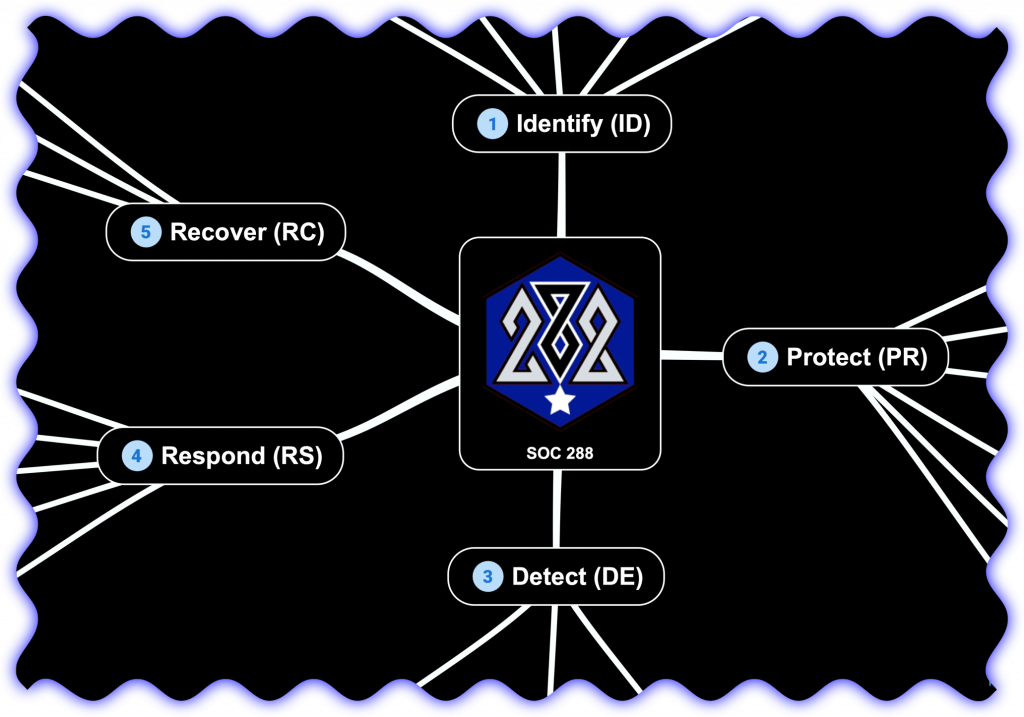
The Security Operations Center (SOC) has five Cyber Security Strategic Objectives. Those objectives based off of the NIST CyberSecurity Framework and are Identify, Protect, Detect, Respond, Recover. The SOC operates as a command center in a similar fashion to a US Army Tactical Operations Center (TOC). The SOC is equipped with advanced technologies, tools, and skilled personnel dedicated to protecting the information systems and sensitive data for Post 288.
Objective 1 – IDENTIFY
This phase involves understanding and managing cybersecurity risks by identifying critical assets, systems, and data, and establishing a baseline of Post 288’s current cybersecurity posture. It includes activities such as asset management, analyzing the business environment, compliance with state regulations, risk assessment, managing supply chain risks, and creating an inventory of cybersecurity-related policies and procedures.
Objective 2 – PROTECT
This phase focuses on implementing safeguards to protect critical assets and data from cybersecurity threats. This includes measures such as access controls (both physical and digital), encryption, secure configurations, employee awareness training, and implementing a vulnerability management program.
Objective 3 – DETECT
This phase involves developing and implementing capabilities to identify and detect cybersecurity events in a timely manner. This includes establishing continuous monitoring processes, implementing IDS/IPS, and conducting regular security assessments and monitoring of systems and networks.
The SOC continuously monitors the organization’s network, systems, and applications using a variety of security tools, such as Endpoint Detection and Response (EDR), Application (layer 7) Firewalls, and Security Information and Event Management (SIEM). This monitoring helps identify suspicious activities, anomalies, or potential security breaches.
When an alert is triggered or a potential security incident is detected, a SOC 288 Analyst investigate and analyze the event to determine its severity, impact, and potential risks to Post 288. They investigate the incident, gather relevant data, and classify it based on the level of threat and priority.
Objective 4 – RESPOND
This phase focuses on establishing an effective incident response and management capability to respond to and mitigate cybersecurity incidents. It includes developing an incident response plan, establishing communication protocols, and conducting drills and exercises to test incident response readiness.
In the event of a confirmed security incident, the SOC takes immediate action to contain, mitigate, and resolve the issue. This involves coordinating with relevant teams, such as network administrators, system engineers, or external incident response teams. The SOC follows predefined incident response plans to ensure a swift and effective response.
The SOC conducts in-depth forensic investigations to determine the root cause of security incidents and breaches. They collect and analyze digital evidence, reconstruct the attack timeline, and provide recommendations to prevent similar incidents in the future.
Objective 5 – RECOVER
This phase involves developing and implementing measures to restore systems, services, and data affected by cybersecurity incidents. This includes creating data backup and restoration processes, conducting post-incident reviews, and implementing improvements to prevent similar incidents in the future.
Roles within SOC 288
The roles found in a Security Operations Center (SOC) and their responsibilities:
- SOC Analyst (SA1): Entry-level SOC analysts are responsible for monitoring security events, triaging alerts, and conducting initial investigations. They assist in incident response efforts and may perform basic security tasks such as vulnerability scanning and log analysis.
- SOC Analyst (SA2): Experienced SOC analysts handle more complex security incidents, conduct in-depth investigations, and provide detailed incident reports. They collaborate with other teams, recommend security improvements, and participate in threat hunting activities.
- SOC Team Leader (TL): The SOC team leader supervise and guide the SOC analysts. They coordinate the daily operations of the SOC, prioritize tasks, allocate resources, and ensure adherence to established procedures and policies. They also liaise with other teams and management to provide updates on SOC activities.
- SOC Manager (SM): SOC managers oversee the entire SOC and are responsible for its strategic direction, budgeting, and resource management. They establish and maintain relationships with stakeholders, develop incident response plans, and make decisions to enhance the overall security posture of Post 288.
- SOC Engineer (SE): The SOC engineers focus on the implementation, configuration, and maintenance of the technical infrastructure within the SOC. They manage security systems, such as the Security Information and Event Management (SIEM), intrusion detection and prevention systems (IDS/IPS), and firewalls. SOC engineers also perform system upgrades, develop automation scripts (PowerShell, BaSH, Python), and troubleshoot technical issues.
- Incident Response Analyst (IRA): Incident response analysts specialize in handling and mitigating security incidents. They lead incident response efforts, coordinate with other teams, and implement containment and remediation strategies. They conduct the After Actions Review (AAR) to identify lessons learned and recommend improvements to prevent future incidents.
Additionally, some SOC team members may conduct other specialized roles such as Threat Intelligence Analysts, Forensic Analysts, or Malware Analysts, depending on Post 288’s needs and resources.
Defensive Areas of Operations (DAO)
- Physical
- Audio Sensors
- Drones
- LPOP (loiter, land to sneak and peek, sensor delivery)
- Anti-drone (jamming, kinetic take down, capture)
- Locks
- Visual Sensors
- IAM
- Authentication
- Authorization
- Endpoint Protection
- Encryption for data at rest
- EDR
- Virus scan
- Network
- Layer 7 Security Appliances
- Layer 4 Firewalls
- Layer 3 switching and segmentation
- Mobile
- Android
- Apple iOS
- VPN
- Remote access
- Site to site
- Wifi
- SaaS Services
- DNS
- instant messaging (aka chat)
- SMS
- Web Servers
- Apache
- IIS
- Web Applications
- DAST/SAST/OSA
- DevSecOps
- Multi-Factor Authentication (MFA)
- Web Application Defense
- WAF
- Geolocation restrictions
- Rate controls
- Reputation
- Data Protection
- Confidentiality
- Integrity
- Availability
- Security Operations Center
- Incident handling
- Logging Aggregation
- Sandbox detonation
- SIEM
- Threat Modeling
- Vulnerability Management
- Eye Candy Dashboards
- Threat Intelligence