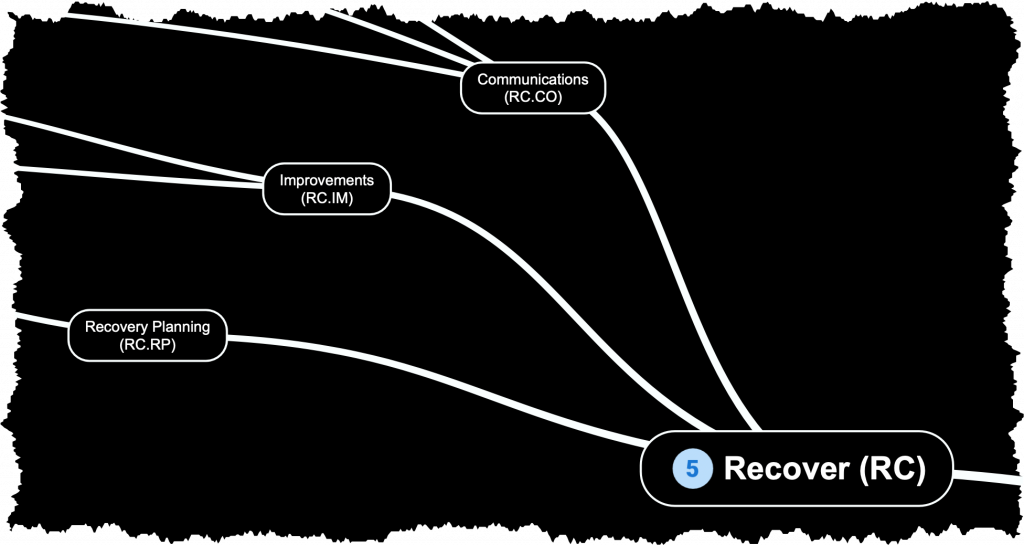
RC – RECOVER
This phase involves developing and implementing measures to restore systems, services, and data affected by cybersecurity incidents. This includes creating data backup and restoration processes, conducting post-incident reviews, and implementing improvements to prevent similar incidents in the future.
Recovery Planning (RC.RP):
Recovery processes and procedures are executed and maintained to ensure restoration of systems or assets affected by cybersecurity incidents.
- RC.RP-1: Recovery plan is executed during or after a cybersecurity incident
Improvements (RC.IM):
Recovery planning and processes are improved by incorporating lessons learned into future activities.
- RC.IM-1: Recovery plans incorporate lessons learned
- RC.IM-2: Recovery strategies are updated
Communications (RC.CO):
Restoration activities are coordinated with internal and external parties (e.g. Internet Service Providers, owners of exploited systems, victims, and vendors).
- RC.CO-1: Public relations are managed
- RC.CO-2: Reputation is repaired after an incident
- RC.CO-3: Recovery activities are communicated to internal and external stakeholders as well as executive and management teams