PR – PROTECT
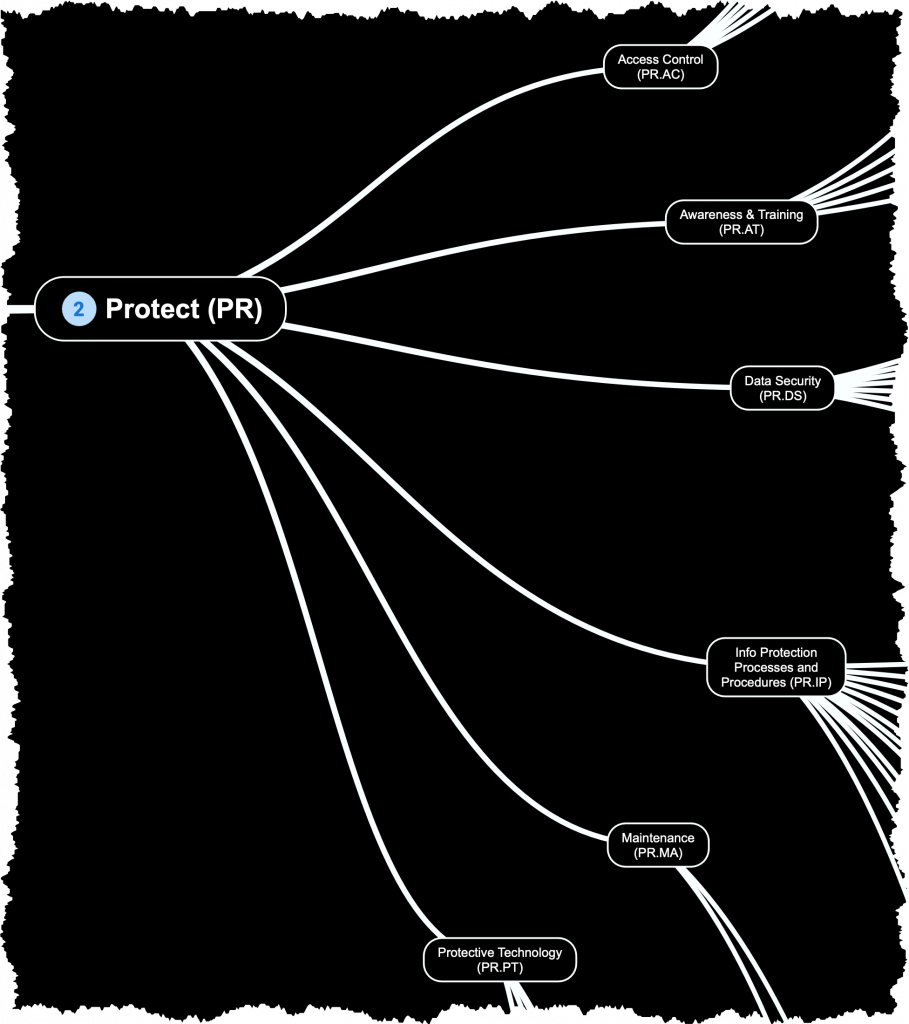
The Protect phase focuses on implementing safeguards to protect critical assets and data from cybersecurity threats. This includes measures such as access controls (both physical and digital), encryption, secure configurations, employee awareness training, and implementing a vulnerability management program.
Access Control (PR.AC):
Access to physical and logical assets and associated facilities is limited to authorized users, processes, and devices, and is managed consistent with the assessed risk of unauthorized access to authorized activities and transactions.
- PR.AC-1: Identities and credentials are issued, managed, verified, revoked, and audited for authorized devices, users and processes
- PR.AC-2: Physical access to assets is managed and protected
- PR.AC-3: Remote access is managed
- PR.AC-4: Access permissions and authorizations are managed, incorporating the principles of least privilege and separation of duties
- PR.AC-5: Network integrity is protected (e.g., network segregation & segmentation)
- PR.AC-6: Identities are proofed and bound to credentials and asserted in interactions
- PR.AC-7: Users, devices, and other assets are authenticated (e.g., single-factor, multi-factor) commensurate with the risk of the transaction (e.g., individuals’ security and privacy risks and other organizational risks)
Awareness and Training (PR.AT):
The organization’s personnel and partners are provided cybersecurity awareness education and are trained to perform their cybersecurity-related duties and responsibilities consistent with related policies, procedures, and agreements.
- PR.AT-1: All users are informed and trained
- PR.AT-2: Privileged users understand their roles and responsibilities
- PR.AT-3: Third-party stakeholders (e.g., suppliers, customers, partners) understand their roles and responsibilities
- PR.AT-4: Senior executives understand their roles and responsibilities
- PR.AT-5: Physical and cybersecurity personnel understand their roles and responsibilities
Data Security (PR.DS):
Information and records (data) are managed consistent with the organization’s risk strategy to protect the confidentiality, integrity, and availability of information.
- PR.DS-1: Data-at-rest is protected
- PR.DS-2: Data-in-transit is protected
- PR.DS-3: Assets are formally managed throughout removal, transfers, and disposition
- PR.DS-4: Adequate capacity to ensure availability is maintained
- PR.DS-5: Protections against data leaks are implemented
- PR.DS-6: Integrity checking mechanisms are used to verify software, firmware, and information integrity
- PR.DS-7: The development and testing environment(s) are separate from the production environment
- PR.DS-8: Integrity checking mechanisms are used to verify hardware integrity
Information Protection Processes and Procedures (PR.IP):
Security policies (that address purpose, scope, roles, responsibilities, management commitment, and coordination among organizational entities), processes, and procedures are maintained and used to manage protection of information systems and assets.
- PR.IP-1: A baseline configuration of information technology/industrial control systems is created and maintained incorporating security principles (e.g. concept of least functionality)
- PR.IP-2: A System Development Life Cycle to manage systems is implemented
- PR.IP-3: Configuration change control processes are in place
- PR.IP-4: Backups of information are conducted, maintained, and tested
- PR.IP-5: Policy and regulations regarding the physical operating environment for organizational assets are met
- PR.IP-6: Data is destroyed according to policy
- PR.IP-7: Protection processes are improved
- PR.IP-8: Effectiveness of protection technologies is shared
- PR.IP-9: Response plans (Incident Response and Business Continuity) and recovery plans (Incident Recovery and Disaster Recovery) are in place and managed
- PR.IP-10: Response and recovery plans are tested
- PR.IP-11: Cybersecurity is included in human resources practices (e.g., deprovisioning, personnel screening)
- PR.IP-12: A vulnerability management plan is developed and implemented
Maintenance (PR.MA):
Maintenance and repairs of information technology system components are performed consistent with policies and procedures.
- PR.MA-1: Maintenance and repair of organizational assets are performed and logged, with approved and controlled tools
- PR.MA-2: Remote maintenance of organizational assets is approved, logged, and performed in a manner that prevents unauthorized access
Protective Technology (PR.PT):
Technical security solutions are managed to ensure the security and resilience of systems and assets, consistent with related policies, procedures, and agreements.
- PR.PT-1: Audit/log records are determined, documented, implemented, and reviewed in accordance with policy
- PR.PT-2: Removable media is protected and its use restricted according to policy
- PR.PT-3: The principle of least functionality is incorporated by configuring systems to provide only essential capabilities
- PR.PT-4: Communications and control networks are protected
- PR.PT-5: Mechanisms (e.g., failsafe, load balancing, hot swap) are implemented to achieve resilience requirements in normal and adverse situations